Tycoon2FA - MFA Is No Longer A Silver Bullet
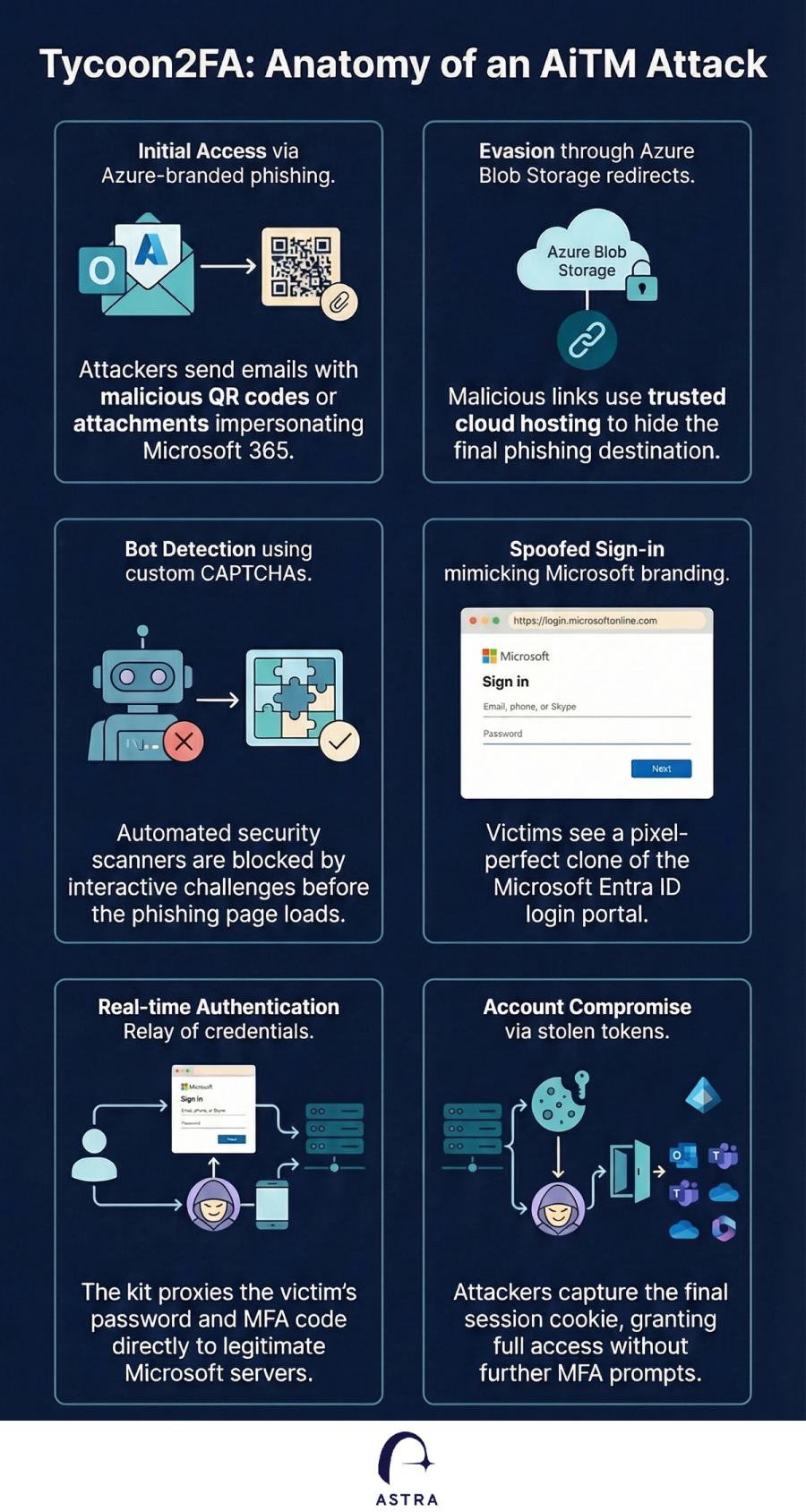
Microsoft Threat Intelligence has uncovered the inner workings of Tycoon2FA, a sophisticated Phishing-as-a-Service (PhaaS) platform that has targeted over 500,000 organizations monthly. Developed by the threat actor Storm-1747, this kit provides Adversary-in-the-Middle (AiTM) capabilities, allowing even low-skill attackers to bypass multifactor authentication (MFA) at scale.
Microsoft Threat Intelligence has uncovered the inner workings of Tycoon2FA, a sophisticated Phishing-as-a-Service (PhaaS) platform that has targeted over 500,000 organizations monthly. Developed by the threat actor Storm-1747, this kit provides Adversary-in-the-Middle (AiTM) capabilities, allowing even low-skill attackers to bypass multifactor authentication (MFA) at scale.
Why Tycoon2FA is a significant threat:
- Massive Scale: It has been responsible for tens of millions of phishing messages across nearly every sector, including healthcare, finance, and government.
- AiTM Sophistication: By intercepting session cookies during the login process, attackers gain full access to accounts and can maintain persistence even after a password reset.
- Evasion Tactics: The kit uses heavy code obfuscation, custom CAPTCHAs, and browser fingerprinting to dodge automated security scanners.
- Fast-Moving Infrastructure: Its domains often last only 24-72 hours, making traditional blocklists less effective.
While Microsoft’s Digital Crimes Unit (DCU) recently collaborated with Europol to disrupt Tycoon2FA’s infrastructure, the rise of such tools highlights an urgent need to evolve our defenses.
Microsoft's Key Recommendations:
- Adopt Phishing-Resistant MFA: Transition to passwordless methods like FIDO2 security keys, Windows Hello for Business, or Microsoft Authenticator passkeys.
- Secure Privileged Roles: Enforce phishing-resistant MFA specifically for admin roles in Microsoft Entra ID.
- Immediate Incident Response: If a compromise is detected, immediately reset credentials and revoke all active sessions and tokens.
- Audit for Persistence: Review affected accounts for malicious inbox rules or unauthorized changes to payroll and financial configurations.
- Enable Advanced Protections: Use Microsoft Defender features such as Safe Links, Safe Attachments, and Zero-hour auto purge (ZAP) to neutralize threats before they reach users.
- User Training: Implement Attack Simulators to train employees on identifying sophisticated lures, including those using QR codes.
How Can Astra Help?
Astra customers can use the built in use cases to identify any privileged users that might be vulnerable to Adversary-in-The-Middle attacks.
Contact us for inquiries or a demo https://astrasec.io/#cta